Mastering Observability in Spring Boot
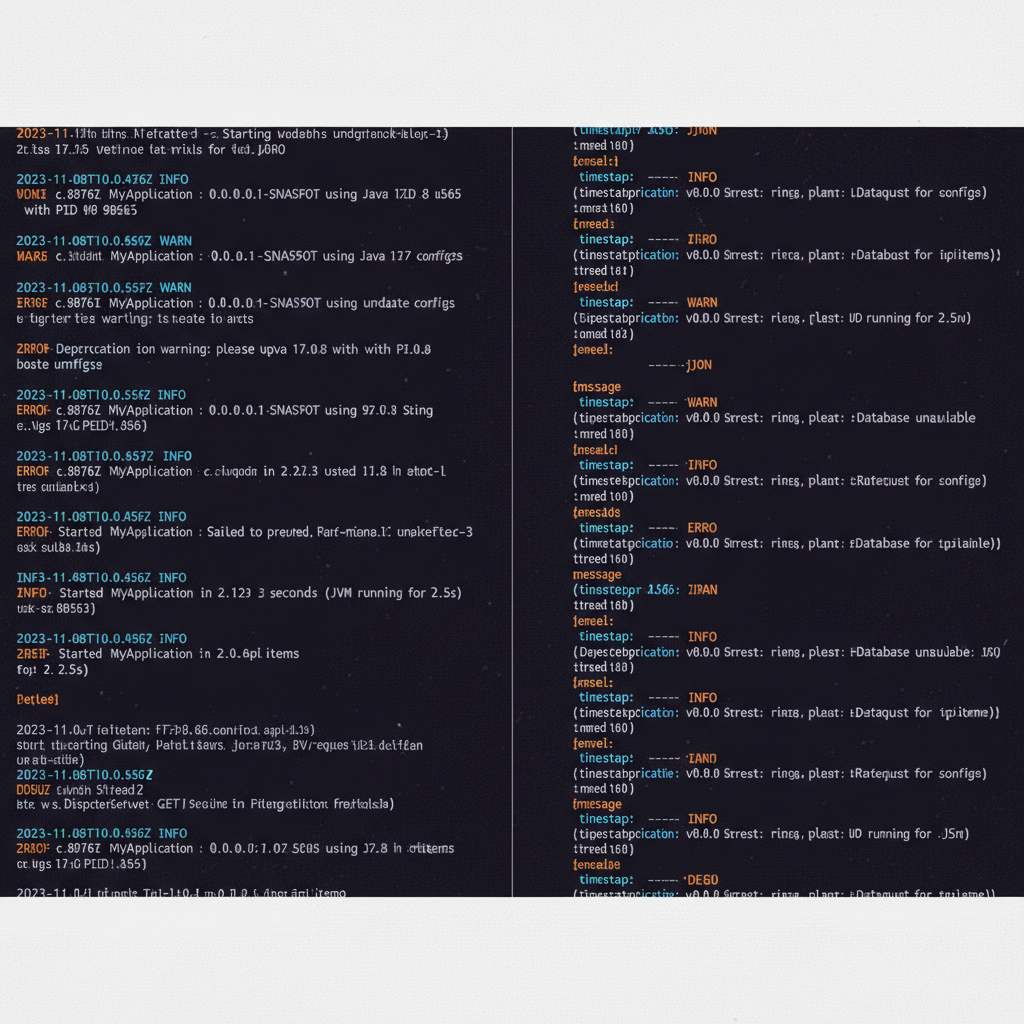
In my experience building distributed systems, logs are often the only window we have into a failing production environment. Yet, many teams treat logging as a secondary concern. Implementing spring boot logging best practices early in your development cycle can save hours of frustration during a midnight P1 incident. When logs are structured, contextual, and performant, they transform from a wall of text into a powerful diagnostic tool.
1. Use the SLF4J Abstraction
Spring Boot uses Logback as its default logging provider, but you should always code against the Simple Logging Facade for Java (SLF4J). By using org.slf4j.Logger, you decouple your code from the underlying implementation. This makes it easier to switch providers or integrate with other spring boot monitoring tools without refactoring your entire codebase.
import org.slf4j.Logger;
import org.slf4j.LoggerFactory;
public class OrderService {
private static final Logger log = LoggerFactory.getLogger(OrderService.class);
}2. Externalize Configuration with logback-spring.xml
While application.properties is fine for basic settings, production-grade apps require a dedicated logback-spring.xml file. This allows you to use Spring-specific extensions like <springProfile>, which lets you define different logging behaviors for ‘dev’, ‘staging’, and ‘prod’ environments. I always recommend keeping console logging for local dev and file/socket logging for production.
3. Adopt Structured JSON Logging
Human-readable logs are great for local debugging, but they are a nightmare for log aggregators like ELK or Splunk. One of the most critical spring boot logging best practices is switching to structured JSON logging in production. This allows your log aggregator to index fields like userId or executionTime as searchable attributes rather than raw strings.
4. Leverage Mapped Diagnostic Context (MDC)
In a multi-threaded environment, it’s hard to track a single request’s path. MDC allows you to inject contextual data—like a Request ID or User ID—into every log statement within a thread’s lifecycle. As I’ve discussed in my guide on distributed tracing with spring boot, correlating logs across services is impossible without a shared trace ID stored in the MDC.
MDC.put("requestId", "abc-123");
try {
log.info("Processing payment");
} finally {
MDC.clear();
}5. Use Parameterized Logging (Avoid Concatenation)
Never use string concatenation in your logs. Not only is it less readable, but it also incurs the cost of string construction even if the log level is disabled. Use the SLF4J placeholder syntax instead:
// BAD
log.debug("User " + user.getId() + " logged in.");
// GOOD
log.debug("User {} logged in", user.getId());6. Set Appropriate Log Levels
I frequently see developers logging everything at INFO level. This creates noise and increases storage costs. Follow these standards:
- ERROR: The system cannot continue. Needs immediate attention.
- WARN: Something unexpected happened, but the system is still running.
- INFO: Significant lifecycle events (startup, shutdown, major state changes).
- DEBUG: Information useful for developers during troubleshooting.
When reviewing spring boot monitoring tools, you’ll find that clear level separation is key to setting up meaningful alerts.
7. Mask Sensitive Data (PII)
Logging raw passwords, credit card numbers, or PII (Personally Identifiable Information) is a massive security risk and a compliance violation. Use Logback’s ReplaceCompositeConverter or a custom masking library to redact sensitive patterns from your logs before they ever hit the disk.
8. Implement Asynchronous Logging
Logging to a file or a network socket is an I/O operation that can block your application threads. For high-throughput apps, use Logback’s AsyncAppender. It buffers log events and writes them on a separate thread, ensuring that your business logic isn’t slowed down by the logging subsystem.
9. Include Versioning and Environment Metadata
When you have dozens of microservices, knowing exactly which version of the code produced a log is vital. Include the git.commit.id and the environment name in your log metadata. This is a foundational step for effective distributed tracing with spring boot deployments where multiple versions might co-exist during a canary release.
10. Avoid Logging the Entire Stack Trace for Business Errors
For expected business exceptions (like UserNotFoundException), logging the entire stack trace is overkill. It bloats the logs and provides no extra value. Only log the full stack trace for unexpected system errors where you actually need to see the code path to the failure.
Common Logging Mistakes to Avoid
In my audits of backend systems, I often see the following pitfalls:
- System.out.println: These don’t go through the logging framework, can’t be formatted, and are synchronous. Never use them.
- Over-logging: Logging every loop iteration or every database call will degrade performance and fill up your disk.
- Ignoring Log Rotation: Without a proper rotation policy (e.g., daily or 100MB limit), your server will eventually crash due to a full disk.
Check your current setup against these spring boot monitoring tools to see if your log volume is within healthy limits.
Measuring Logging Success
How do you know if your spring boot logging best practices are working? Look for these metrics:
- Mean Time to Recovery (MTTR): Does your logging allow you to find the root cause of an error in minutes rather than hours?
- Log Search Latency: Are your logs structured so that your log aggregator can return results instantly?
- Storage Cost vs. Value: Are you spending a fortune to store DEBUG logs that no one ever looks at?
Effective logging is a cornerstone of distributed tracing with spring boot. If you can follow a request across three microservices using a single Trace ID, you’ve succeeded.
